Microsoft Defender for Endpoint: Overview, Features & Benefits
Table of Contents
Introduction
In today’s dynamic, changing cybersecurity environment, organizations face an increasing number of security threats. While effective in protecting against known malware, traditional antivirus solutions are inadequate to cope with the complex demands of contemporary business.
Developing advanced threats like zero-day, fileless, and complex phishing attacks calls for business organizations to have a more comprehensive and proactive security solution.
Microsoft Defender for Endpoint (MDE) has been built to tackle these new security needs by implementing robust defensive capabilities, detection controls, and response features for endpoint security.
What is Microsoft Defender for Endpoint (MDE)?
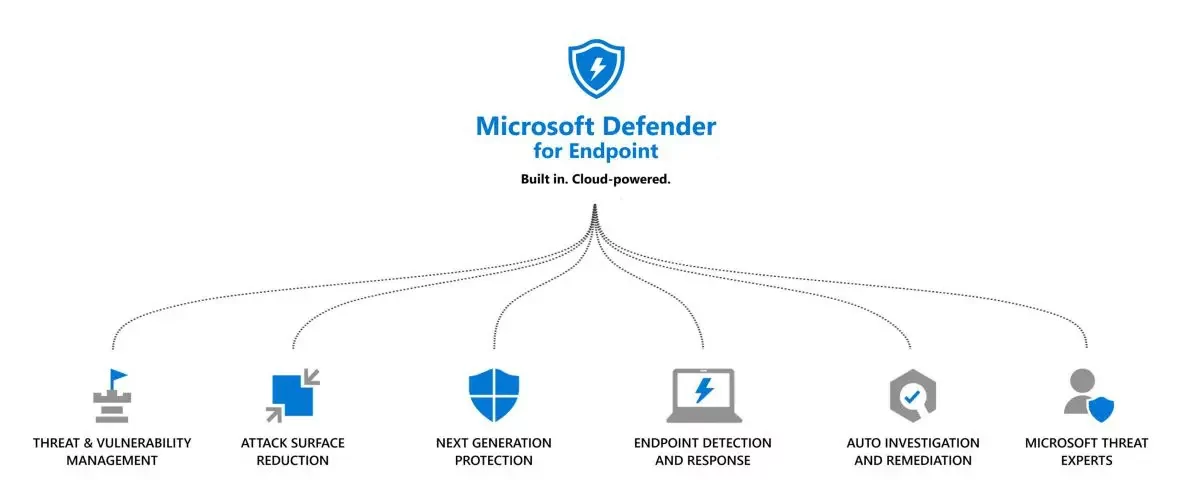
Microsoft Defender for Endpoint, or Windows Defender ATP, is a powerful security product for enterprise networks that protects diversified endpoints like desktops, laptops, servers, and mobile phones. MDE is a comprehensive Microsoft Defender product showcasing tremendous integration with Microsoft 365 security solutions, Azure Active Directory, and other Microsoft security solutions.
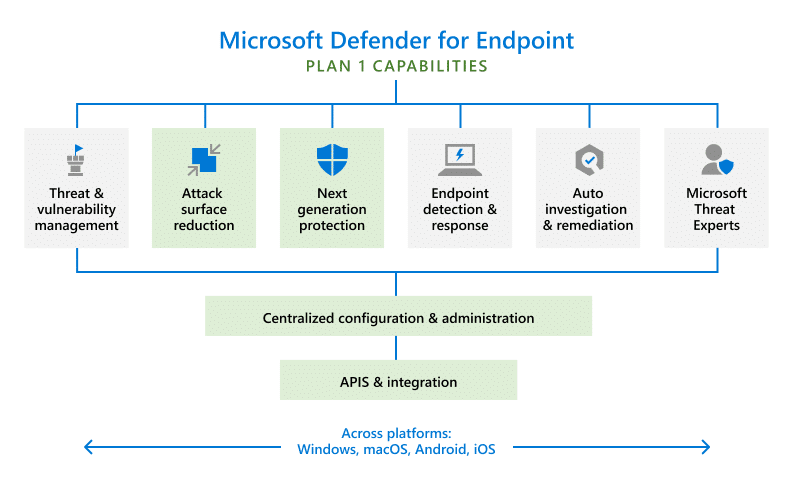
MDE combines multiple layers of security tools and functions into one platform that offers holistic protection for endpoints. It uses sophisticated antivirus technologies, endpoint detection and response (EDR) capabilities, and automated investigative and remediation capabilities to defend against the full spectrum of cybersecurity threats.
Key Features of Microsoft Defender for Endpoint
1. Next-Generation Antivirus (NGAV):
NGAV for MDE can detect and prevent known and unknown malware in real-time. Unlike conventional signature-based antivirus products, NGAV utilizes machine learning, behavioral analysis, and cloud-based intelligence to detect and prevent threats from occurring before they can cause harm.
2. Endpoint Detection and Response (EDR):
EDR is an integral component of MDE, enabling organizations to identify, track, and investigate endpoint suspicious behavior. Through EDR, security teams can track incidents, identify attack patterns, and receive detailed information regarding malicious activity. MDE’s EDR component enables organizations to react quickly to incidents and prevent further loss.
3. Automated Investigation and Remediation:
Microsoft Defender for Endpoint automatically investigates and resolves security incidents. When a suspected threat is identified, MDE automatically initiates investigations, examines the relevant data, and identifies the source of the incident.
Furthermore, if necessary, MDE automatically takes remedial measures to correct the problem, including isolating an infected system from the network or preventing the execution of malicious files.
4. Threat and Vulnerability Management:
5. Unified Security Management Console:
Microsoft Defender for Endpoint provides a built-in security management portal that allows security staff to track and manage endpoint security across the organization. The portal provides a holistic view of security issues, threats, and device state, thus allowing teams to respond better to incoming threats.
6. Threat Intelligence and Cloud Security:
7. Microsoft 365 Defender integration:
Why Microsoft Defender for Endpoint?
Organizations increasingly seek MDE due to its robust security features and integration with existing Microsoft infrastructure. With over 25.8% of the global endpoint security market share, Microsoft Defender for Endpoint is the most widely adopted solution for protecting multi-platform enterprise environments, surpassing all other vendors in customer usage.
A few of the main reasons organizations should deploy MDE are:
- Holistic Safeguarding: MDE provides multi-layered security above and beyond regular antivirus protection. Through NGAV, EDR, vulnerability management, and remediation automation, MDE gives top-to-bottom protection against known and unknown threats.
- Scalability: Whether you operate a small or large organization, MDE can be customized to suit the organization’s needs. MDE is designed to support devices ranging from desktops to laptops, mobile devices, and servers, and hence, it is a perfect match for organizations of any size.
- Seamless Integration with Microsoft Ecosystem: MDE is natively integrated with other Microsoft solutions, such as Azure Active Directory, Microsoft Intune, and Microsoft 365 Defender. This integration allows users to manage security across the organization from a single console.
- Advanced Threat Protection: MDE leverages artificial intelligence and machine learning technologies to detect and block advanced threats like fileless malware and zero-day attacks. The platform’s threat protection capabilities ensure your endpoints are always protected against the latest attack methods.
- Centralized Security Management: MDE offers an integrated interface to manage and monitor endpoint security across the enterprise. The interface supports security teams in acquiring end-to-end visibility of potential threats, vulnerabilities, and security events, thereby facilitating the investigation and response process for security events.
- Cloud-Driven Security: With Microsoft’s cloud platform, MDE offers real-time security and the most current threat intelligence. Cloud-based protection allows MDE to immediately detect and block new threats in real time, ensuring endpoints are secured from even the most sophisticated attacks.
As security operations matured in 2025, automated investigation and AI-supported analysis became essential for helping teams prioritize incidents and respond efficiently at enterprise scale.
Simplify Endpoint Protection with Expert-Led MDE Deployment
From policy configuration to SIEM integration and remediation automation, our expert team ensures a smooth and secure rollout of MDE tailored to your compliance and operational needs.
Request a ConsultationYou may also like: Understanding Microsoft Defender Offerings for Enhanced Security
The Place of MDE in the Broader Business Security Landscape
Although MDE’s primary concern is endpoint security, it is extremely valuable in the overall security context.
With the integration within other Microsoft security offerings and services, including Microsoft Sentinel (SIEM), Microsoft Defender for Identity, and Microsoft Defender for Office 365, MDE offers a comprehensive framework for a cybersecurity strategy.
With the combined security solution, organizations can achieve end-to-end visibility into their security posture and enhance their threat response capabilities.
Benefits of Microsoft Defender for Endpoint:
- Reduced Security Incident Opportunities: By offering sophisticated threat detection, response, and remediation capabilities, MDE drastically minimizes the likelihood of data and security breaches. Its proactive defense controls enable organizations to get in front of attackers, effectively preventing potential breaches before they can happen.
- Enhanced Incident Response: The remediation and investigation capabilities offered automatically by MDE improve response efficiency against security breaches. The improvement reduces response time to contain and remedy the breaches, thus minimizing the possible damage.
- Cost-Effective Security: MDE provides a holistic array of functionalities, serving as a singular solution for securing endpoints. This integration negates the necessity for various unrelated security instruments, lowering the total expenditure associated with cybersecurity and improving protective measures.
- Improved Adherence: MDE supports organizations in meeting a variety of compliance requirements by enabling in-depth security logs, audit trails, and reporting. This is vital for regulated industry companies, where requirements such as GDPR, HIPAA, and PCI-DSS compliance must be met.
From Endpoint Protection to Security Signal Orchestration
As enterprise security strategies mature, endpoint protection is increasingly viewed as one component of a broader detection and response framework rather than a standalone control. In this context, Microsoft Defender for Endpoint functions as a high-fidelity signal source within Microsoft Defender XDR, supplying rich endpoint telemetry that can be correlated with identity, email, SaaS, and cloud security signals.
This shift reflects a broader move toward unified detection and response, where the effectiveness of endpoint security is measured not only by what it blocks, but by how well it supports investigation, prioritization, and coordinated response across the organization. By contributing trusted endpoint insights into a centralized security model, Defender for Endpoint helps teams move from isolated alerts to clearer, context-driven security decisions.
Further Reading: Microsoft Defender for Endpoint: Features and Capabilities
Integrate MDE Seamlessly with Microsoft Sentinel & Defender Suite
Get more from your Microsoft investments. We connect Defender for Endpoint with SIEM, email, and identity protections to deliver a unified threat response across the enterprise.
Request a ConsultationWhat This Means for Organizations Moving Into 2026
As organizations move into 2026, security priorities are increasingly shaped by the operational lessons of 2025. While detection capabilities across enterprise environments have matured, many teams continue to face challenges related to alert volume, investigation effort, and response consistency. This has shifted the focus from adding more security tools to improving how security data is correlated, interpreted, and acted upon.
In this context, Microsoft Defender for Endpoint supports a broader move toward integrated, outcome-driven security operations. Endpoint telemetry is no longer valuable in isolation; its impact comes from how effectively it contributes to unified investigation workflows, clearer prioritization, and faster, more coordinated response across identity, email, cloud, and application environments.
Looking ahead, organizations are prioritizing security platforms that enable scalability, automation, and AI-assisted analysis without increasing operational complexity. As security teams prepare for 2026, the ability to translate high-volume security signals into actionable insight will remain a defining factor in building resilient, efficient, and sustainable security operations.
Conclusion
In the ever-evolving world of cyber threats, Microsoft Defender for Endpoint offers a solid solution to safeguard endpoints from a wide range of malicious behavior.
Next-gen antivirus, EDR, automated investigation, vulnerability management, and Microsoft Defender for Endpoint allow organizations to identify risk, detect, and respond, and automate response actions.
For companies that must protect their digital assets, MDE offers end-to-end protection, native integration in the Microsoft ecosystem, and cloud-based intelligence that keeps them ahead of cybercriminals at all times.
MDE deployment bolsters endpoint protection and improves overall security posture, allowing companies to combat the ever-changing cyber threat landscape.
FAQs
Microsoft Defender for Endpoint provides strong endpoint protection, but its greatest value is realized when it operates as part of a broader Microsoft security ecosystem. Organizations typically see the best outcomes when endpoint signals are correlated with identity, email, cloud, and application data through Microsoft Defender XDR to support faster investigation and coordinated response.
Defender for Endpoint integrates natively with Microsoft tools such as Microsoft Entra ID, Microsoft Defender for Office 365, Intune, and Microsoft Sentinel. For organizations with mixed environments, it can also coexist with other security solutions, allowing teams to consolidate visibility and improve response workflows without replacing everything at once.
As organizations move into 2026, the primary benefits are operational rather than purely technical. These include reduced alert fatigue, faster incident triage through automated investigation, improved prioritization of threats, and more consistent response across endpoints and user environments. The focus shifts from managing tools to managing outcomes.
Deployment complexity depends on the size of the environment and existing security maturity. While Defender for Endpoint is cloud-based and integrates well with Microsoft 365, organizations often require planning around policies, onboarding workflows, role-based access, and SIEM integration to ensure it operates effectively at scale.
Yes. Defender for Endpoint supports compliance initiatives by providing detailed security logs, audit trails, and reporting capabilities. These features help organizations meet regulatory requirements such as GDPR, HIPAA, and PCI-DSS by improving visibility, traceability, and incident response documentation.
Organizations should consider expert support when they want to optimize Defender for Endpoint beyond basic deployment. This includes aligning it with broader security operations, integrating with SIEM and XDR workflows, reducing operational overhead, and preparing security teams for AI-assisted investigation and 2026-ready security models.